Introducing The Forrester Model To Defend Against Nation-State Threats
Given years of cyberespionage, attacks on elections, and, more recently, the melding of kinetic and digital warfare in the Russia-Ukraine war, private sector security leaders in all industries must recognize and prepare for more brazen and frequent nation-state cyberattacks.
This is the first and the foundational report in a series that will help security leaders build a practical defense against nation-state activity.
Nation-State Cyberattacks And Subsequent Regulations Are Complex And Accelerating
Globalization and the internet brought the most powerful nations closer together. Now, geopolitical tension driven by a tug of war between authoritarianism and democracy are pulling them back apart. The internet is splintering along national borders, and with it, organizations are being forced by governments wary of national security concerns to choose sides. Cyberattacks and their effects on the private sector are central to this new conflict given the profound impact that they can have on vital national services. This surfaces new challenges for businesses, such as:
- An increase of nation-state cyberattacks, as well as those targeting the private sector. According to data from the Council on Foreign Relations, about 40% of reported cyberoperations by country target the private sector, and state-sponsored attacks have increased by almost 100% between 2019 and 2022.
- Fraught motivations, implications, and attributions for cyberattacks. Attacks in the cyberdomain are strategically ambiguous — they’re difficult to attribute, tend to be abstract, have indirect outcomes (e.g., if a hospital is hit by a ransomware attack and a person dies, who’s responsible?), and have unclear escalation paths (what recourse does a private business have on a nation-state attacker?).
- Market moves that undermine geopolitical influence instigating cyberattacks. Businesses have been targeted with cyberattacks because their intent to expand operations doesn’t fit with national interests. Every multinational enterprise must be prepared for this kind of scrutiny and potential blowback as they move into new markets.
- National-security-related cyberincidents exposing enterprises to undue ramifications. Private businesses must be adept at managing requests related to national security from federal and local governments in the event of a breach by balancing appropriate disclosure with avoiding self-incrimination.
- Litigation for inaction and a lack of pre-breach preparation on the horizon. In 2022, the Federal Trade Commission warned companies to patch Log4j or face potential legal ramifications. These steps by governments will continue and become more comprehensive as governments encourage organizations to adopt more robust security capabilities.
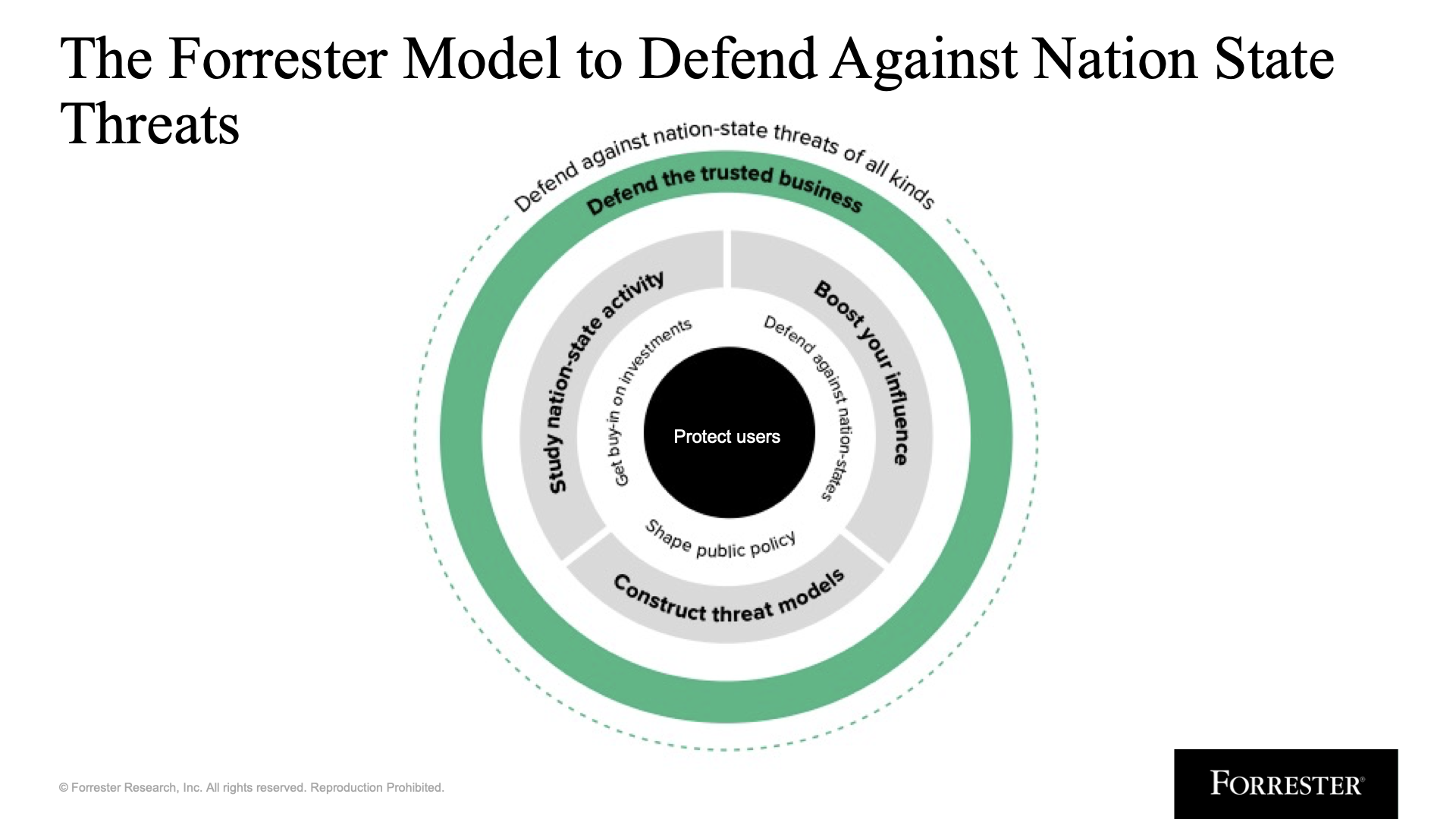
These factors led us to create a new model, The Forrester Model To Defend Against Nation-State Threats. This model is a strategic view of everything that security teams need to do to defend the business against nation-state threats of all kinds — cyberattacks or subsequent regulatory challenges. The report details tactical recommendations for each piece of the model. This research helps security leaders:
- Develop an informed defense against nation-state attacks. Defending against nation-state attacks requires security teams to build threat models, validate defensive measures, and establish runbooks built for organization-specific threat activity and fallout.
- Enter and exit new markets with confidence. Preparing for cyberattacks as a business enters a new market is often the last concern on the list, but it shouldn’t be. Enterprises can make the transition to or from markets a smoother process by understanding and preparing for the geopolitical implications and potential blowback.
- Shape future policy that will affect the business. Public policy and regulatory efforts on information security are emerging, which makes this a prime time for enterprises to influence its direction via lobbying and other measures before policies are set in stone.
- Secure buy-in for strategic, high-impact defense investments. There are few initiatives that get as much attention from the board as looming government oversight. Security leaders can leverage this attention to get buy-in for security initiatives such as implementing Zero Trust; enabling governance, risk, and compliance; and enhancing security operations.
Read the full report to learn more about the model and get tactical recommendations on how to approach them. Also, if this topic interests you or you have questions, reach out to me via inquiry or on LinkedIn.