Choose Your Own Adventure With The 2014 Verizon DBIR
In a world where every single security vendor has their own annual threat report, the Verizon Databreach Investigations Report (DBIR) is the gold standard, and this year is no different. Last year I began blogging my initial analysis (Observations on the 2013 Verizon Data Breach Investigations Report), and I wanted to continue that again this year. Here are some of the high-level details on this year's report:
Last year I began blogging my initial analysis (Observations on the 2013 Verizon Data Breach Investigations Report), and I wanted to continue that again this year. Here are some of the high-level details on this year's report:
- Fifty organizations representing 95 countries were included in the data set. This included 1,367 confirmed data breaches. By comparison, last year’s report included 19 organizations and 621 confirmed data breaches.
- In a significant change, Verizon expanded the analysis beyond breaches to include security incidents. As a result, this year’s dataset has 63,437 incidents. This is a great change, recognizes that incidents are about more than just data exfiltration, and also allows for security incidents like DoS attacks to be included.
- The structure of the report itself has also evolved; it is no longer threat overview, actors, actions and so on. One of the drivers for this format change was an astounding discovery. Verizon found that over the past 10 years, 92% of all incidents they analyzed could be described by just nine attack patterns. The 2014 report is structured around these nine attack patterns.
- The DBIR has always been known for its humor, and the lulz continue in the 2014 report. There are references to Breaking Bad, The Princess Bride, as well as the Dos Equis commercials. The "Miscellaneous Errors" recommendations section had me laughing out loud. I think this tone is very important; reading a 50-page report shouldn't require Ritalin and restraints.
Before I move on, I wanted to point out one painfully shocking statistic. Figure 13 contrasts how long it takes the attacker to compromise an asset and how long it takes the defender to discover it. The trend lines "show that attackers are getting better/faster at what they do at a higher rate than defenders are improving their trade." Attackers are able to compromise assets in days or less well over 75% of the time while defenders struggle to detect in days or less at 25% of the time. Keep in mind, this is over the past decade; these are not encouraging data points.

HOW TO USE THE 2014 DBIR
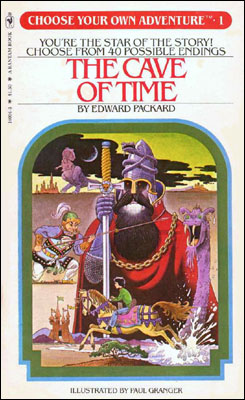 Do you remember the Choose Your Own Adventure books from the '80s and '90s? I have fond memories of reading these books as a child. If you are not familiar with them, they are unique in that the reader becomes the main character and gets to actually guide the actions and outcome of the book. The book is customized to the reader. So what does this have to do with the DBIR? Let me explain. I started off the blog mentioning that every single vendor has some sort of annual report that they publish. If you are like me, you don't have time to read them all. Many of these reports are macro focused, and while some *might* be helpful in your day-to-day job most are not. Most of the reports lack relevancy to your organization. With the DBIR's pivot to attack patterns, you can now read the DBIR like a Choose Your Own Adventure book. Here is the obvious use case:
Do you remember the Choose Your Own Adventure books from the '80s and '90s? I have fond memories of reading these books as a child. If you are not familiar with them, they are unique in that the reader becomes the main character and gets to actually guide the actions and outcome of the book. The book is customized to the reader. So what does this have to do with the DBIR? Let me explain. I started off the blog mentioning that every single vendor has some sort of annual report that they publish. If you are like me, you don't have time to read them all. Many of these reports are macro focused, and while some *might* be helpful in your day-to-day job most are not. Most of the reports lack relevancy to your organization. With the DBIR's pivot to attack patterns, you can now read the DBIR like a Choose Your Own Adventure book. Here is the obvious use case:
- Check out the North American Industry Classification System (NAICS) to understand how you industry is classified within the DBIR. This may be apparent to most, but there are some industries where it isn't clear.
- Go to Figure 19, "Frequency of incident classification patterns per victim industry," and select your industry. I've selected "Education" for this example.
- Pick out the top incident patterns that apply to your industry. The leading patterns for education are: Everything Else, Misc Error, Web App Attack, and Theft/Loss.

- Now you can focus on what is most relevant to your organization. Use this data for presentations to senior management. Build these incident patterns into your threat model. You do have a threat model, correct? How do your security controls line up with Verizon's recommendations?
- I do have one word of caution for you. Verizon included Figures 69 and 70, which mapped SANS Critical Security Controls to incident patterns. If you look across Table 69, you will see that Incident Response (IR) is only mapped to DoS attacks and Skilled Staff is mapped only to Cyber Espionage. Don't read this as a suggestion that you don't need IR or skillse staff for other incident patterns. All organizations, regardless of industry or incident patterns, need IR and skilled staff.
I am a big fan of the new structure of the DBIR; the 2014 DBIR has transitioned from a report to a tool. Other vendors should consider taking a similar approach. What would really be cool is if Verizon provided a web-based interface that allowed you to input your specifics and have a customized report generated for you. Speaking of suggestions for Verizon, last year I wrote:
"I would like to see Verizon break out of breaches and incidents that resulted from third parties. Using the Verizon threat actor definition, I’d specifically like to see data on external threat actors who compromised companies via third-party networks. For example, I want to know how many organizations were attacked via an extranet connection to a supply chain partner. Third-party risk is a top concern of Forrester clients."
My request around greater detail into third-party incidents/breaches stands. Third-party risk was a top concern before the Target breach, and anxiety around it has only increased since. You could even "Choose your own adventure" around a business partner and see what the most likely incident patterns are for that organization and then question them specifically around how they are mitigating that risk.
Finally, I have a question for you. Can you generate similar data for the incidents that have occurred in your organization? What are your top incident patterns? Are you tracking time to compromise and time to discovery? You don't have to use the VERIS format to describe incidents, but you need to use something.