“Alexa, Stop Leaking My Data.” — How Consumer Smart Devices Threaten Company Assets
Most of us have heard about the vulnerabilities in smart devices that enable hackers to spy on, and communicate with, unsuspecting victims. While regulators struggle to standardize security requirements for the internet-of-things (IoT) market, companies and their employees remain vulnerable to a slew of unsecured devices. Considering the consumer IoT market is expected to grow to $143.5 billion annually by 2025, it’s clear enterprises must have a strategy to deal with this unmitigated risk- but most don’t.
In our most recent study on the security of consumer IoT devices, we explored how consumer IoT devices expand the attack surface of organizations dealing with an influx of these unmanaged devices into their ecosystem. We found that smart devices suffer from several security flaws that allow hackers to threaten enterprise data and assets. For instance, poor authentication schemes, which made headlines for being one of the main causes of the Mirai botnet attack, can also allow hackers to move laterally through the local network, thus giving a foothold into corporate assets. IoT companion apps suffer from the same vulnerabilities as other web-based apps, which provide attackers with another avenue into mobile devices. Voice assistants, which can be found in nearly 50% of US households, are currently susceptible to laser-based local exploits.
Your Employees Are Interacting With An Ever-Expanding Ecosystem Of Insecure IoT Devices
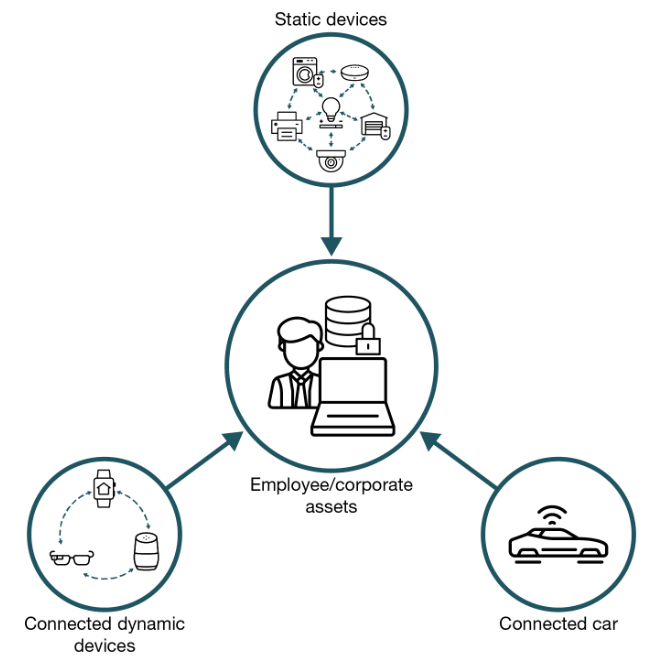
In our report, we break down the IoT market into three distinct categories to better outline the most common threat vectors faced by enterprises. Static devices, like printers and smart TVs, are often left in home networks, while dynamic devices, like wearable health trackers and smart speakers, can travel between home and office networks. The final smart device category is the modern connected car, whose increased computational horsepower increases the risks typically found in other dynamic devices. In our report, we dive into how each of these types of devices pose distinct risk profiles from IP theft to potential ransomware attacks on a company. It’s our hope that this research will lay the groundwork for further discussions regarding how security and risk professionals can harden their networks to the threats posed by the growing IoT market through improvements to internal policies around BYOD, work-from-home best practices, and security technology adoption.
(Written with Benjamin Corey, research associate at Forrester)