Regulators Are Moving On SBOMs — But Is Your Compliance Program Keeping Pace?
Software bill of materials (SBOM) requirements are advancing rapidly, and the time for “wait and see” is quickly running out. The global regulatory landscape for software supply chain security is shifting from recommendations to mandates, yet many organizations remain unprepared. What you do now will determine whether your company is ready or left behind as SBOM mandates solidify.
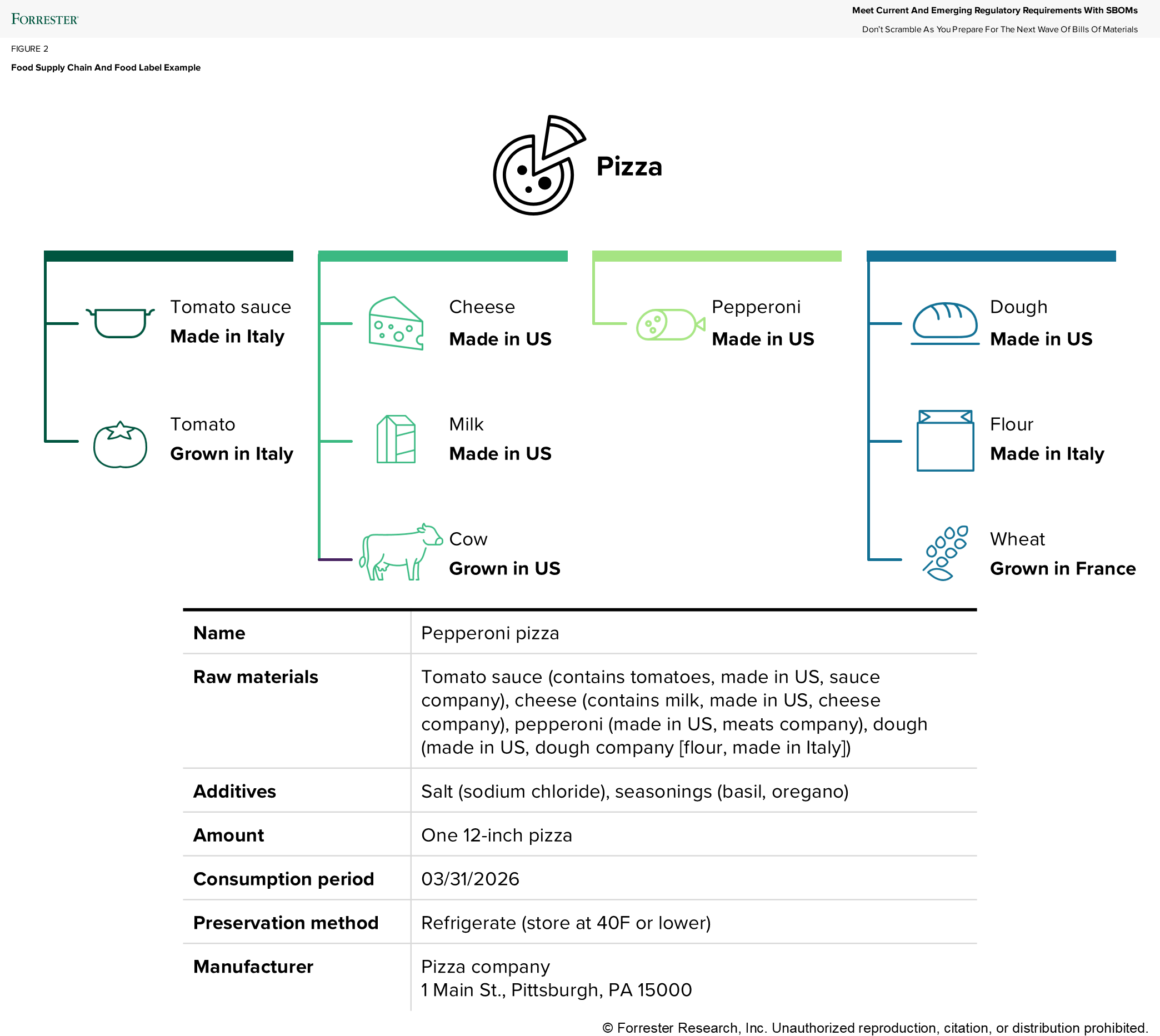
Behind The Sauce: What A Pizza Label Teaches Us About Software
A pizza nutrition label, for example, provides transparency about ingredients and sourcing, aids recalls, alerts about potential allergies, and informs consumer choices. Similarly, an SBOM acts as a “digital ingredient label,” listing software components, origins, and dependencies. Both promote supply chain transparency, enabling rapid responses to risks, such as contamination or vulnerabilities, while fostering trust and proactive risk management.
SBOMs Move From Best Practice To Baseline, But The Path Isn’t Straight In The US
SBOMs have evolved from a cybersecurity best practice to a baseline expectation with the publishing of Executive Order 14028 that emphasized the need for stronger software supply chain security. Congress mandated SBOMs for medical devices under the Food and Drug Omnibus Reform Act, requiring manufacturers of “cyber devices” to submit detailed software information to the FDA. The Department of Defense and the Army have also integrated SBOMs into procurement processes with the Software Fast Track Initiative supporting risk assessments and vendor security practices using SBOMs. Despite progress, the US regulatory landscape remains inconsistent. White House policy has shifted, rolling back Office of Management and Budget memoranda that required secure software attestations and SBOM centralization across agencies. Instead, a decentralized, risk-based approach has emerged. This uncertainty leaves suppliers guessing, with no unified playbook.
Global SBOM Mandates Raise The Stakes And The Standard
While US policy remains fluid, global SBOM momentum is accelerating. The European Union’s Cyber Resilience Act introduces mandatory cybersecurity and vulnerability management requirements for products with digital elements. Manufacturers must identify and document software components and vulnerabilities, with SBOMs positioned as a must for vulnerability reporting starting September 11, 2026, alongside a requirement to produce and maintain SBOMs by December 27, 2027. South Korea has outlined a roadmap to expand SBOM adoption across public sector systems, while Japan and Australia are embedding SBOMs into critical infrastructure guidance. India’s CERT-In is promoting software supply chain security through national cybersecurity directives, particularly in government and critical sectors. Internationally, SBOM readiness is essential for regulatory compliance, vulnerability management, and access to regulated markets.
Customers Begin To Demand SBOMs, Too
Enterprises are prioritizing secure software development and SBOMs in procurement, often including SBOM requirements in RFIs or in contracts to demand transparency from vendors. SBOMs help assess risks, identify vulnerabilities, and manage open-source license obligations.
Three Steps To Be SBOM-Ready Now
These three steps are not exhaustive, but they will significantly boost your program. At a minimum, you must:
- Inventory your software supply chain. Identify all software your organization uses, develops, sources, or provides, including the development tool chain, open source tools and plug-ins, third-party libraries and components, SaaS, third-party APIs, and internal builds. Determine the supplier, owner, and origin of each software component. You will need an inventory to prioritize which components are critical for managing, requesting, and producing SBOMs.
- Automate SBOM creation in development. Integrate SBOM generation into your DevSecOps pipeline using software composition analysis tools. Automated SBOM creation ensures that every release includes up-to-date, standards-based SBOMs (e.g., CycloneDX, SPDX) without adding manual overhead. You will be ready when customers or mandates require an SBOM on demand.
- Securely manage and operationalize SBOMs. Establish processes to update SBOMs as software evolves, and archive past versions for compliance. You’ll be ready when the next zero-day vulnerability gets announced and can use the SBOM to target where in your software it exists.
Build SBOM Capabilities Before Mandates Arrive
Waiting for uniform policies is a losing strategy — agility and readiness are now competitive differentiators. Start building SBOM capabilities today, including inventory, automation, and management. These steps will position your organization to meet regulatory demands, reduce supply chain risk, and earn trust with regulators and customers. It will also help prepare you for the future, with emerging “ingredients lists” such as cryptographic BOMs, AI BOMs, and SaaS BOMs expected to follow quickly. Forward-thinking organizations are already exploring these to stay ahead of future regulatory requirements. Read my new report, Meet Current And Emerging Regulatory Requirements With SBOMs, for more information on regulatory requirements and how to meet them with SBOM management, and schedule a guidance session to learn more.
