The Colonial Pipeline Cyberattack Is A (Another) Call For Zero Trust And Resilience In Industrial Companies
On Friday, May 7, 2021, Colonial Pipeline safely shut down its pipeline operations due to a ransomware incident in its corporate network. Colonial Pipeline transports 45 percent of the fuel along the East Coast of the United States through 5,500 miles of pipeline. To mitigate the disruption of Colonial Pipeline, the US government allowed a temporary hours of service exemption for trucks transporting fuel, but many states in the Southeast USA still experienced fuel shortages this week. The incidents of the past week have confirmed the lack of cyberresilience in many industrial companies and is another reminder of the benefits of Zero Trust in mitigating the effects of ransomware.
The Industrial Community Must Improve Resilience In Operational Networks Using Zero Trust Strategies
Digital transformation (or IT/OT convergence, or Industry 4.0, or whatever your chosen buzzword is) has been great for industrial companies’ ability to deliver products efficiently and reliably. But we have collectively failed to appreciate how fragile these systems are and how easy it is for cybercriminals to affect business operations and potentially create unsafe conditions in industrial environments. Colonial Pipeline isn’t the first time ransomware or destructive malware in a corporate network has disrupted or degraded industrial operations, and sadly, it will not be the last. Over the last few years, Norsk Hydro, Honda, Merck, Maersk, Johannesburg’s electric utility, and other industrial companies have all seen ransomware significantly affect their core business operations. For companies with significant industrial operations, corporate IT should be viewed as the “add-on,” not the main network.
OT Should Function Without IT
Operational technology is where a business makes money. If petroleum flows, turbines spin, and assembly lines move, then a company can withstand a breach in the corporate IT environment and continue to serve customers and partners. Furthermore, a breach in OT should not shut down all of OT. Some social media pundits have criticized Colonial for not “air gapping” its business and industrial networks. As explained at length by my friend Joe Slowik, air gaps are not practical or required outside very few scenarios, usually around nuclear energy. With a Zero Trust strategy primarily focused on protecting industrial processes, industrial companies are better positioned to withstand a ransomware attack and maintain operational uptime.
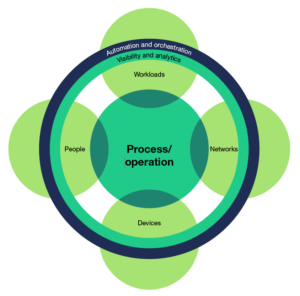
IT and business leaders likely have heard myths that a Zero Trust architecture is too costly or complex. In reality, organizations can implement many ZT strategies with current technology and updated policies and standards. For example, using unique identities to access critical information or processes doesn’t require new technology. Baselining industrial automation systems and configuring allow lists so that only authorized systems can communicate with them is a great strategy to reduce the risk of a cyber-physical attack. You can find our full Zero Trust implementation guide on our client portal.
My colleagues Allie Mellen and Steve Turner have blogged separately about ransomware-specific defenses here.
