RSA Conference 2020: An Intelligence Nerd’s Shopping List
RSA Conference is an incredible opportunity for vendors to showcase their products and services to the security and risk community. Vendors, my shopping list does not include vaporware or snake oil. Everyone attending knows the internet is a scary place and threats are around every digital corner. Skip the scary statistics, and tell me how your tools are going to help end users reduce risk to their customers and employees.
For a refresher on what security and risk areas I cover, please see my introductory blog. My shopping list for RSAC 2020 includes:
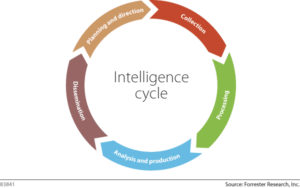
- Threat intelligence platforms that an analyst can use throughout the entire intelligence cycle. A tool that only helps with one of the steps in the intelligence cycle is of marginal use to an intelligence analyst.
- Intelligence providers that put client requirements first. Producing intelligence without alignment to consumer requirements is a waste of time. Show me how you elicit and manage client intelligence requirements.
- For industrial control system (ICS) security vendors, I want to find out how your products aim to improve operations (efficiency and productivity) while protecting processes (safety and reliability).
- Vulnerability risk management tools that can automate the safe patching of IT assets.
- Digital risk protection services that cyber threat intelligence, physical security, antifraud, insider threat, social media, marketing, and corporate communications teams all share. It shouldn’t need to be repeated, but security and risk is a team sport.
- Vendors that understand the lexicon of security and risk. For example, threat != vulnerability. To claim that your tools model cyberthreats when they are really just identifying potentially exploitable code is sad.
In between the plethora of vendor expo briefings, I plan on learning the latest and greatest research on ICS and supervisory control and data acquisition (SCADA) security so I can better serve those security and risk professionals.
The first presentation I plan on watching is The Journey of Cybersecurity in Kuwait’s Oil and Gas Industry from Dr. Reem Al-Shammari, the CISO of Kuwait Oil Company. She will present an information security governance framework for a large ICS asset owner within a complex and dangerous threat landscape.
Next up on my schedule is SCADA/ICS Inherited Insecurity: From Nuclear Power Plants to Oil Rigs from Aleksander Gorkowienko of Spirent Communications. He’ll discuss his research on practical exploitation techniques of SCADA systems and include a live demo. If you’re willing to do a live demo at an enormous security conference, you must be exceptionally smart or brave. Either way, I’m sure it’ll be interesting!
After seeing a live demo of ICS vulnerability exploitation, I’m going to head to a hands-on ICS event led by David Formby and Caleb Purcell at Gaming the Control System. They’ll have a 3D virtual lab that allows you to manipulate human-machine interfaces and programmable logic controllers.
If you can’t get a seat at Robert M. Lee’s keynote, a great alternative is likely Operational Technology (OT) and Industrial Cybersecurity Best Practices from John Johnson at Deloitte to talk about asset identification and threat response in operational technology and industrial internet-of-things environments.
In addition to ICS research, I’m planning on one intelligence-focused presentation from Filip Stojkovski, threat intelligence manager at Adobe. He’s presenting his LEAD intelligence framework for use cases beyond the security operations center, incident response, and threat hunting teams. As I’m doing some research on operationalizing intelligence for strategic security and risk leaders, I’m hoping to get a different perspective with this talk.
When I’m catching up on sleep on my flight back to the East Coast, I expect to have learned from the presenters and vendors how the industry has gotten more mature regarding cyber threat intelligence and ICS security. I’m also hoping I won’t be joking about another security snake oil salesman.
