Navigate China’s New Data And AI Regulations
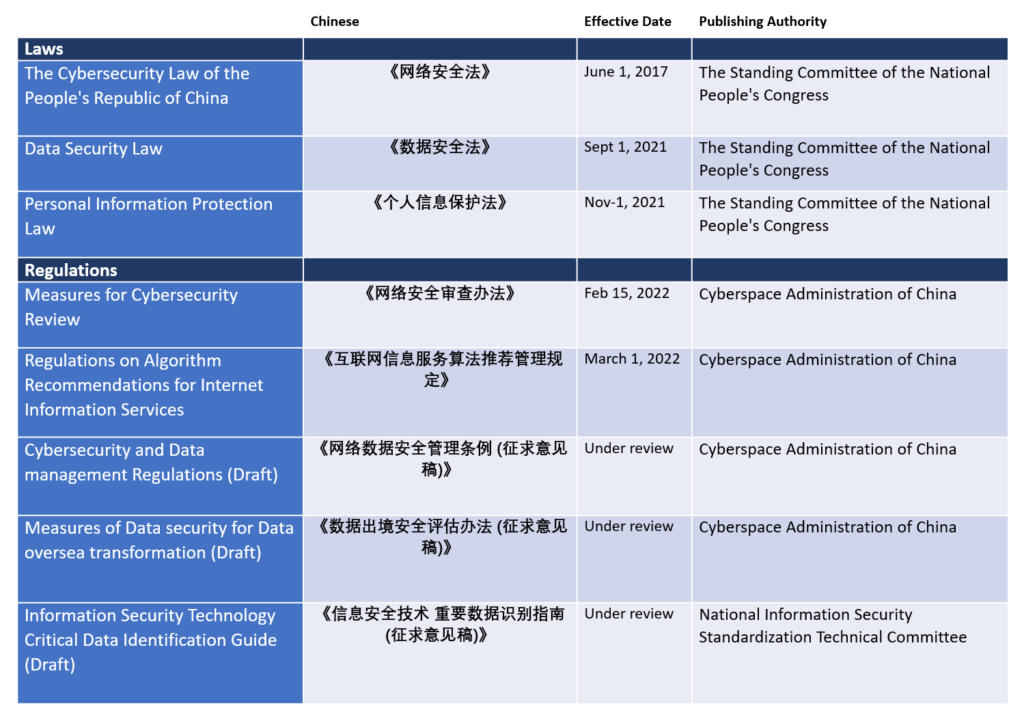
Government-led data privacy and security consultations gave birth to new regulations over the past six months in China. While these are starting to be enforced, 2022 will see the launch of even more data-related regulations (Figure 1). Firms operating in China are looking for guidance on how to adjust their data-related policies, as they need to swiftly navigate a fast-changing regulatory environment. Here are three areas to focus on:
- The data security law means broad changes to firms’ operations. The 2017 cybersecurity law provided little guidance on application scenarios. The 2021 data security law brings much-needed clarity on how the law will be enforced and what compliance means for firms. The Measures for Cybersecurity Review draft clarifies that firms with more than 1 million users must seek approval from the government before launching an IPO abroad. The Cybersecurity and Data Management Regulations draft calls for implementing necessary data security controls, incident response measures, notification of data subjects within three working days in addition to other notification obligations, established channels for data security complaints, and more. Regarding critical data, a data classification and grading system will be established in coming months. Currently, firms can classify their data based on the draft of Critical Data Identification Guide, which is released for public review, but the final version is subject to change.
- The Personal Information Protection Law (PIPL) requests more transparency and user consent. The law states that operators should offer accurate description when requesting consent, and individuals have the right to withdraw their consent. Many internet services have either updated their usage terms or requested reauthorization for different services in the same app. WeChat has repositioned their opt-out options to a clear profile setting page. Firms need to accommodate their recommendation services and monetization strategies with less data features available. Firms should also refer to the same evaluation to adapt internal policies when processing employee personal information.
- The new regulation on algorithm recommendations requires ethical use. Starting March 1, the new regulation requires recommendation services to be moral, ethical, fair, accountable, and transparent. Algorithm models cannot induce users to indulge or overconsume. Firms cannot leverage user preference to offer unreasonable differential treatments, such as trading prices. Firms may need to design new ways to display, sort, and filter information. Some internet firms should assess their business models and pricing strategies. The regulation requires that service providers inform users of the purpose and intention of their algorithms. Firms should be more transparent on their consent terms or offer new ways to inform users.
How Should You Respond?
In a fast-changing regulatory environment, firms often struggle to identify the appropriate security controls and practices to meet compliance. Consequently, many firms chose to slow down product and service development, waiting to gain clarity on execution standards and application details. Firms can refer to Forrester’s cybersecurity and privacy playbook to increase their oversight competency. There are three practices we recommend firms adapt during these local trends:
- Self-assess according to the requirements. The fifth clause of the Personal Information Protection Law gives firms a starting point to review data usage. Focus your initial assessment on internal data use and handling practices. Then, expand your view and assess what data you share or exchange with third-party partners and services. The default data-sharing policies and APIs are potential risks.
- Learn from the failures of others. Some internet firms have already received a warning from the China National App Administration Center. For severe cases, firms must suspend and rectify their services, then wait for approval to continuously operate. The warned firms and reasons for warnings are publicly available. Firms should track these cases and take them as examples for internal review periodically.
- Look for new technologies for governance and data protection. Exchange of data between organizations requires more management and monitoring. Enterprises can explore new mechanisms to exchange or modify data with emerging technologies and approaches such as homomorphic encryption, differential privacy, confidential computing, and more.
If you would like to share your best practices regarding privacy and data regulations, please schedule an inquiry (inquiry@forrester.com), or submit a briefing request.
